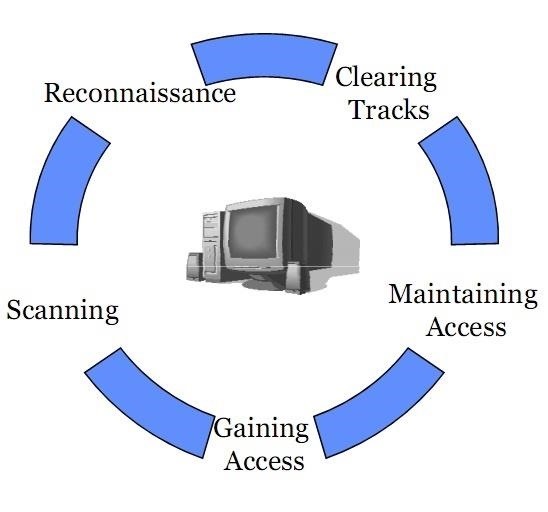
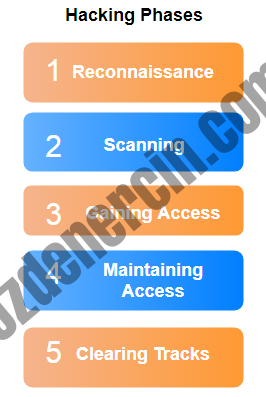
1 cs591 chow Hacking Methodology (Steps) An excellent description inside of the back cover page of “Hacking Exposed” text by McClure et al. Scanning Footprinting. - ppt download

Hacking with AWS: incorporating leaky buckets into your OSINT workflow - Malwarebytes Labs | Malwarebytes Labs